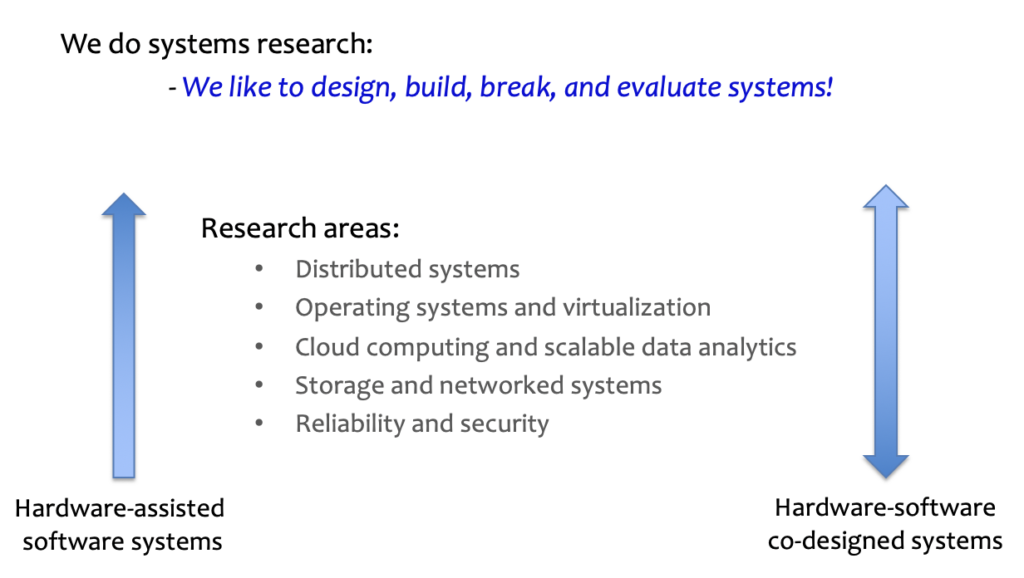
Research Areas
Our research focuses on building efficient, reliable, and secure software systems. To this end, we work at the intersection of operating systems, distributed systems, storage systems, compilers and runtime systems, data analytics systems, and cloud computing.
Interested in working with us?
Please see our active research projects below. If you are interested in working with us, please contact us to enquire about an open research topic.
Active Research Projects

Hardware Security and HW/OS Co-Design
- Minimal silicon root of trust, e.g., OpenTitan
- Trusted execution environment, e.g., AMD Sev, Intel SGX/TDX
- HW/OS design for IoT, data centers, dis-aggregated systems and accelerators ( FPGAs, GPUs, ASICs)
- Minimal hypervisors with trusted boot and remote attestation
For more details, please visit Accelerated Computing Systems Group page.

Operating Systems and Virtualization
- Library OSes / Unikernels (Unikraft)
- Usage of eBPF, MPK, WebAssembly and trusted computing in virtualization/operating systems for improved isolation and security
- Lightweight VMs for Serverless
- Nested acceleration for Smart PCIe devices (SSDs, Smart NICs)
- Containers and orchestration engines (e.g., Kubernetes)
- NixOS and Package Manager (a Linux distribution)
- Data center software systems
- Fast multiplexing of VM network devices
- End-to-end evaluation for networked systems in simulation
For more details, please visit OS and Virtualization Group page.

Accelerated Computing Systems
- Software systems for accelerators (GPUs, FPGAs, TPUs)
- OS support for FPGA-accelerated systems
- Heterogenous acceleator management in the cloud
- I/O acceleration with FPGAs and smart devices (Smart NICs/Smart SSDs)
- Serverless platforms with accelerators (FPGAs, GPUs)
- Infrastructure Processing Units (IPUs) to offload less critical/demanding work
For more details, please visit Accelerated Computing Systems Group page.

Distributed Systems and Cloud Computing
- Replication protocols for fault-tolerance and system scalability
- Usage of trusted computing hardware in distributed systems
- Distributed storage systems, e.g., filesystems, shared log, KV stores, databases
- Data analytics platforms, and serverless systems
- Microservices and Function-as-a-Service (FaaS)
- Local-first software systems using decentralized computing
Team: Martin Kleppmann, Dimitra Giantsidi, Anjo Vahldiek-Oberwagner
Binary Translation and Memory Models
- Binary translation for weak memory architectures (E.g., x86 to Arm/RISC-V)
- Hardware-assisted binary translation, e.g., usage of Arm MTE (Memory Tagging Extensions)
- Static (LLVM), dynamic (Qemu), and hybrid binary translation mechanisms
- Linux kernel memory model (LKMM): Interplay of compiler optimizations on LKMM
For more details, please visit the Binary Translation Group page.

Emerging Memory Technologies
- Persistent memory: programming models, safety and security
- CXL-based systems: Programming model, memory model, performance, fault-tolerance, PCIe modeling
- Heterogenous memory management: Compiler-assisted memory management, programming model, PCIe-based devices
Team: Anatole Lefort, Dimitrios Stavrakakis, Patrick Sabanic
Quantum Software Systems
- Compilers for Quantum Computing
- Quantum Virtual Machine (QVM)
- Quantum Operating System (QOS)
- Hybrid Quantum-Classical Orchestration
- Quantum Error Correction
- Quantum Error Mitigation
Team: Manos Giortamis, Francisco Romão, Aleksandra Świerkowska, Nathaniel Tornow
For more details, please visit the Quantum Software Systems Group page.

Trustworthy Systems: Security & Reliability
- Security and reliability of operating systems
- Cloud systems security
- Confidential computing
- Static and dynamic program analysis techniques, automated testing
- Exploring the compilers’ and CPU architectures’ roles in providing a reliable computing base.
- Security and reliability of Linux kernel along with it its dependencies, in particular toolchains (such as Clang/LLVM and GCC) and languages (C, and more recently Rust)
- Building on memory-safe languages and novel software abstractions (E.g., Cloudflare/Fastly, WebAssembly)
Team: Marco Elver, Martin Fink, Dimitrios Stavrakakis, Patrick Sabanic, Anjo Vahldiek-Oberwagner, Harsha Unnibhavi
For more details, please visit the Trustworthy Systems Group page.
CPU Microarchitecture for Data Centres
- Branch prediction
- Microarchitectural support for context switches
- Instruction delivery
- Front-end bottleneck in server workloads
Team: David Schall
For more details, please visit the CPU Microarchitecture Group page.